How to setup your PBX to go through firewall
In order to have every Ozeki Phone System feature working correctly, you need to configure the firewall on the server machine appropriately. The following guide gives information about how to configure the firewall properly on the machine that runs Ozeki Phone System.
Ozeki Phone System offers a wide range of excellent services. These services use various ports. If these ports are blocked by a firewall, you may experience problems with using Ozeki Phone System - calls may not work, the system cannot access the database (SQL API) or your program cannot send requests to the system (HTTP API).
The main port used by Ozeki Phone System is the 5060 UDP port, by default. This port receives SIP messages from clients - if you close this port, no calls can be made. You can configure the ports used by the system in the System settings menu on the Web-based GUI of Ozeki Phone System.
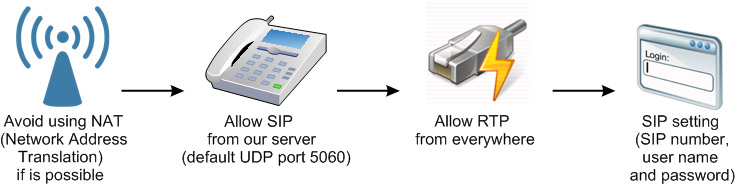
Figure 1 enlists some tips on how to setup your firewall in order to make VoIP calls efficiently:
- If it is possible avoid to use NAT (Network Address Translation)
- Allow SIP from our server (by default, port 5060 is used)
- Allow RTP from all direction
- SIP setting (specify SIP number, username and password)
In order to ensure seamless operation, you need to open the ports on the firewall that are used by the Ozeki Phone System - or by external devices and softwares accessing it.
VoIP and firewall settings in Ozeki Phone System
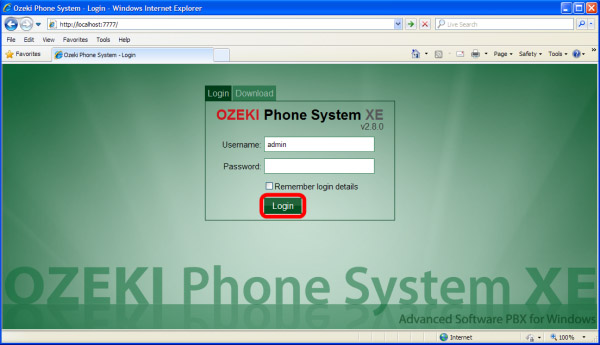
First of all, you need to type in your username and password to login into your Ozeki Phone System (Figure 2).
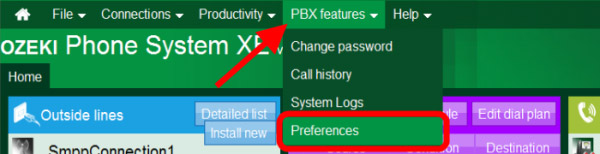
To modify Voip and firewall settings click on PBX features and then Preferences menupoint (Figure 3).
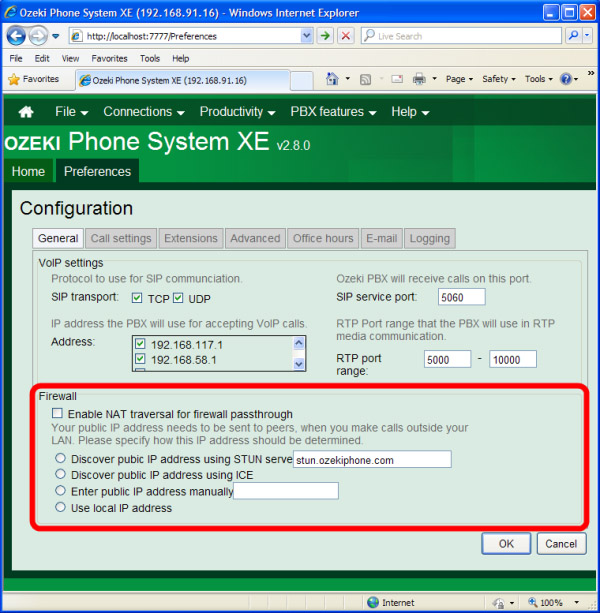
Under the General tab you can modify VoIP settings. If you want to change the default SIP service port (5060) you can do it here easily. Moreover, you can also add new RTP (Real-time Transport Protocol) port range and specify the protocol(s) for SIP communication (TCP or UDP) (Figure 4).
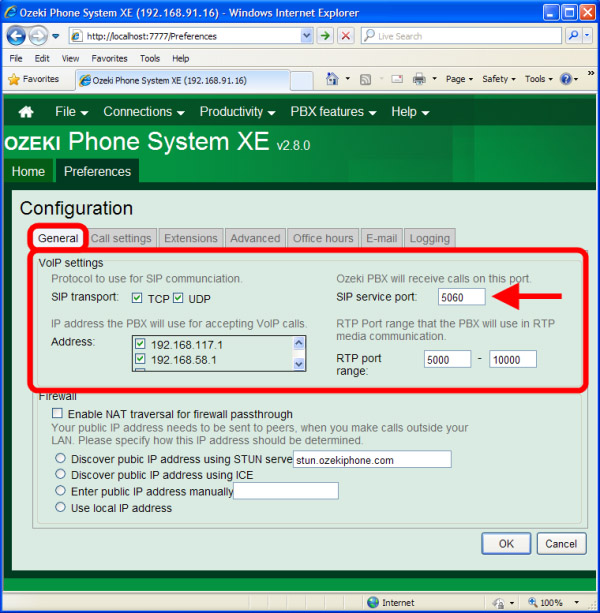
At the Firewall section of the tab, you can make changes in the firewall settings of Ozeki Phone System (Figure 5).
- Enable NAT traversal for firewall passthrough
- Discover pubic IP address using STUN: stun.ozekiphone.com
- Discover public IP address using ICE
- Enter public IP address manually: X.X.X.X
- Use local IP address
NOTE: firewall setting modifications are critical steps. Please make sure that you make the correct modifications - wrong firewall settings can create security holes exposing your system to hackers or malicious software. Please consult with a network administrator when making firewall settings. Open only those ports on the firewall that is used by the system - opening other ports is unnecessary - it is better to keep them closed.
For more information or assistance, please contact us at info@ozekiphone.com
Related pages:
More information
- How to configure telephone system processes
- How to set network resources (IP, ports, protocols)
- Discover services provided by the telephone system
- How to setup your PBX to go through firewall

 Sign in
Sign in